OKTA Integration
Secure search can also be enabled through OKTA, an enterprise-grade identity management service designed for the cloud and compatible with many on-premises applications. Click the link below for more information on OKTA: [Click]
HERE.
Configuring OKTA in SearchBlox
Follow these steps to use OKTA secure search:
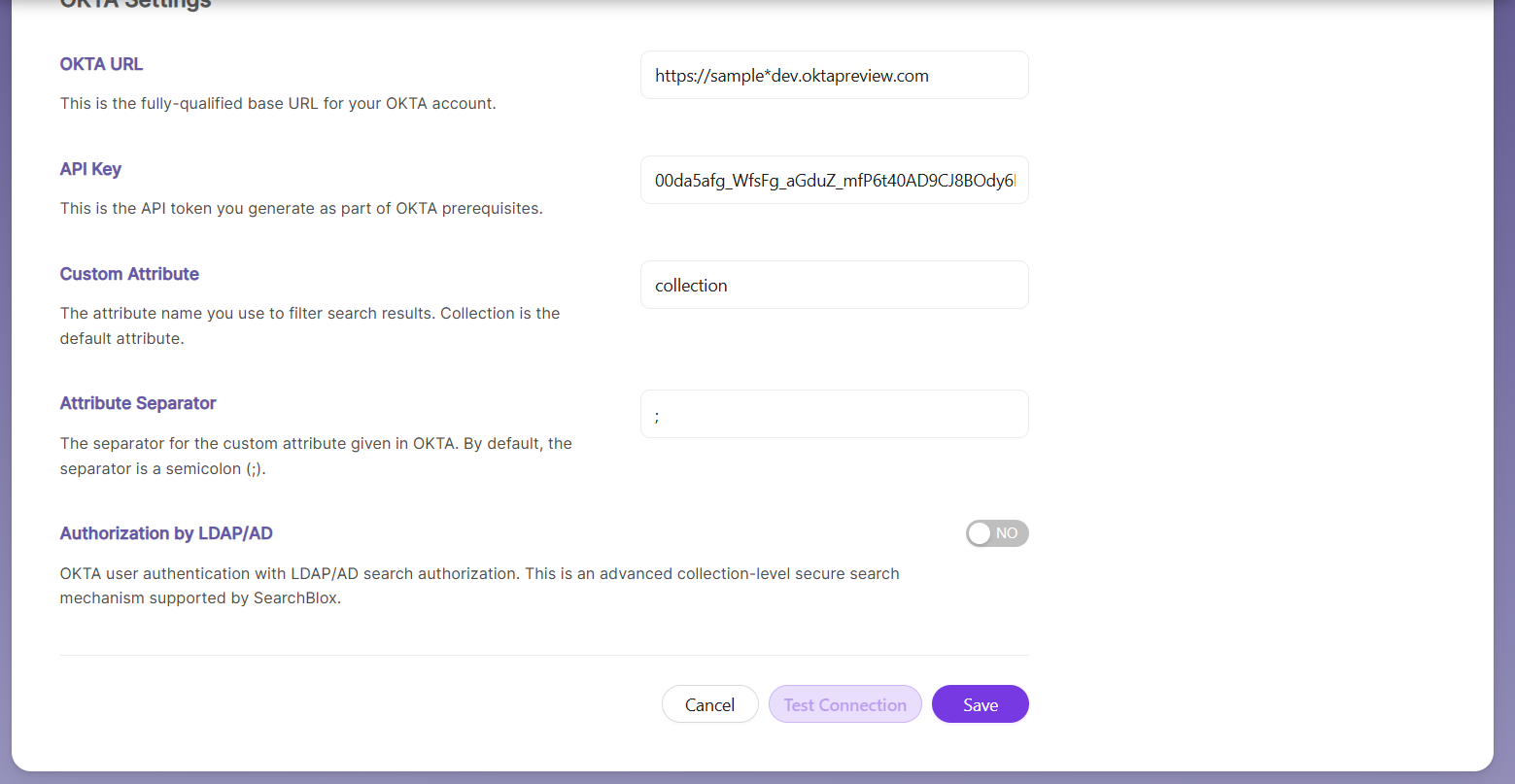
- Select Security Type as OKTA.
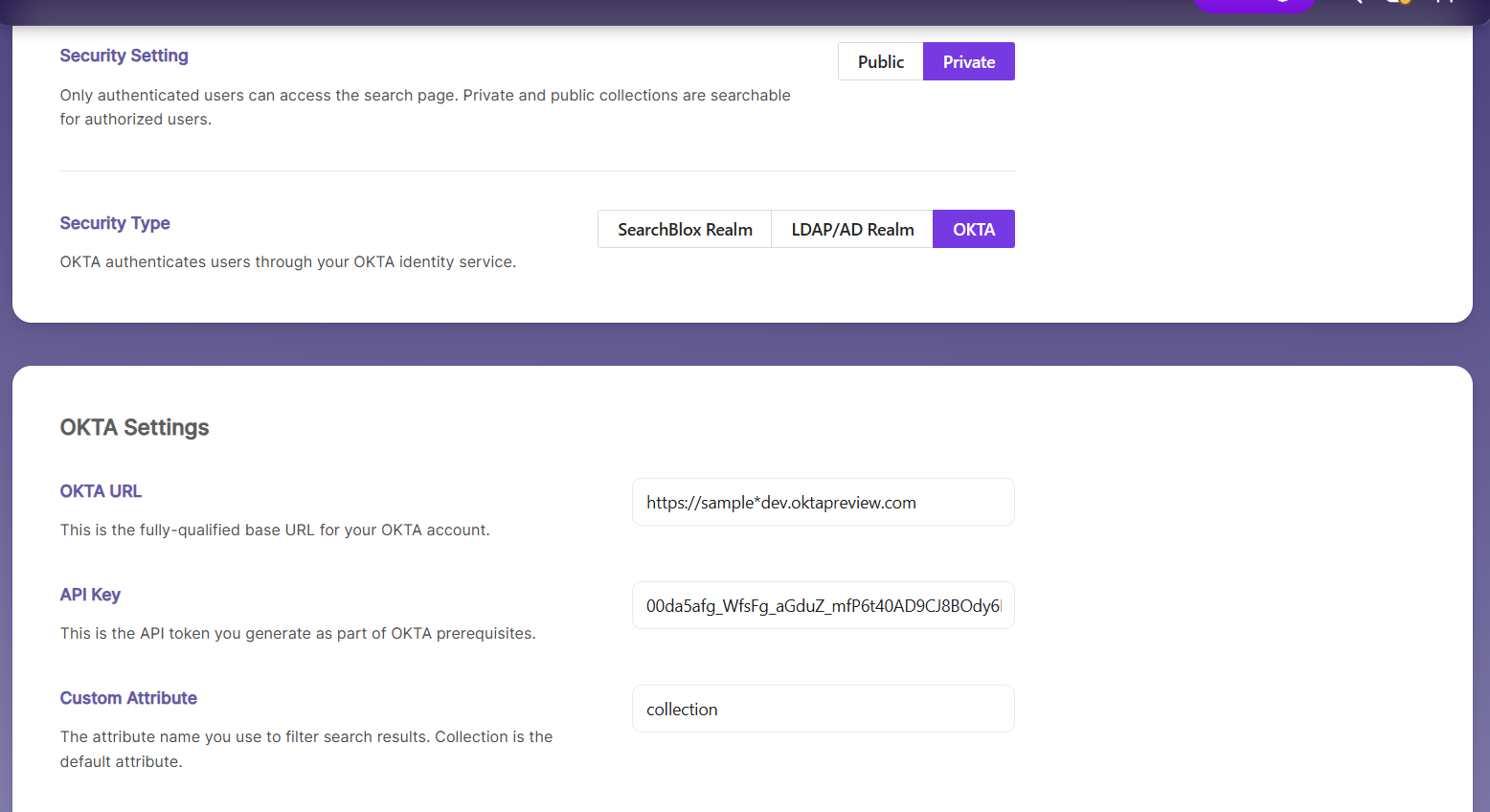
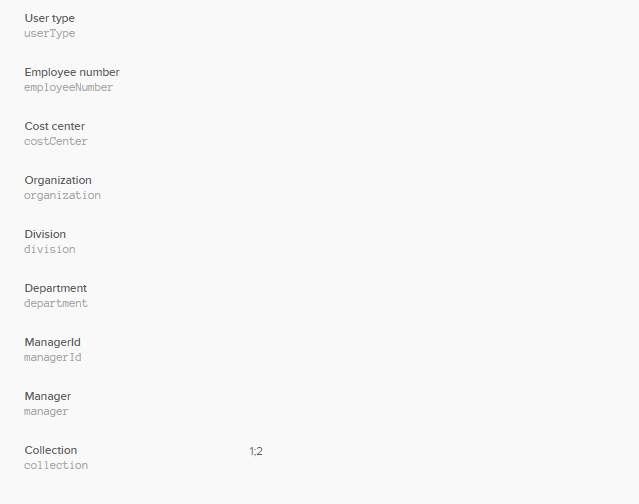
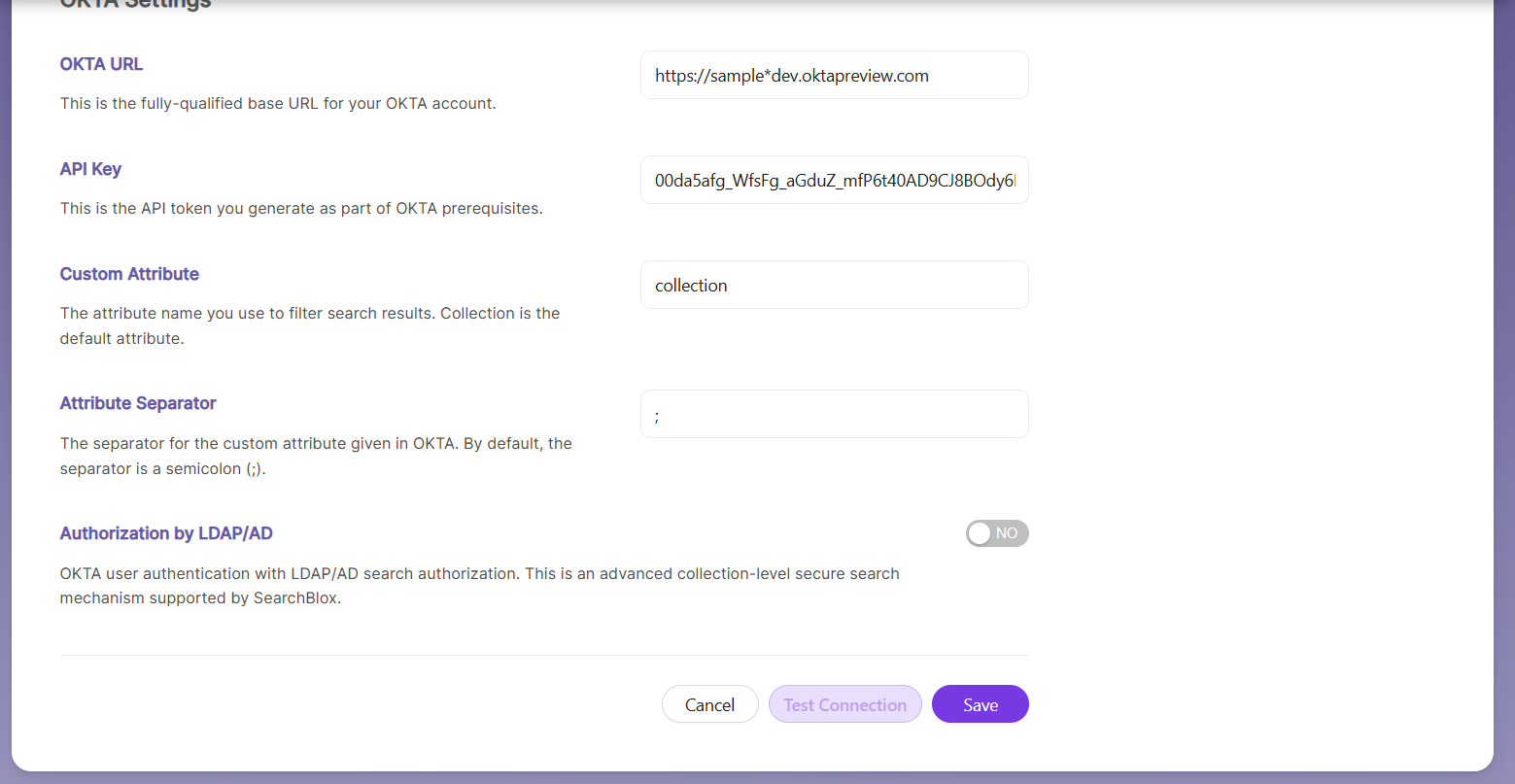
- Enter the required details for OKTA Settings.
| Field | Details |
|---|---|
| OKTA URL | The fully qualified base URL for your OKTA organization. |
| API Key | The API key created earlier as part of the OKTA prerequisites. |
| Custom Attribute | The attribute used to filter search results. By default, this value is Collection. |
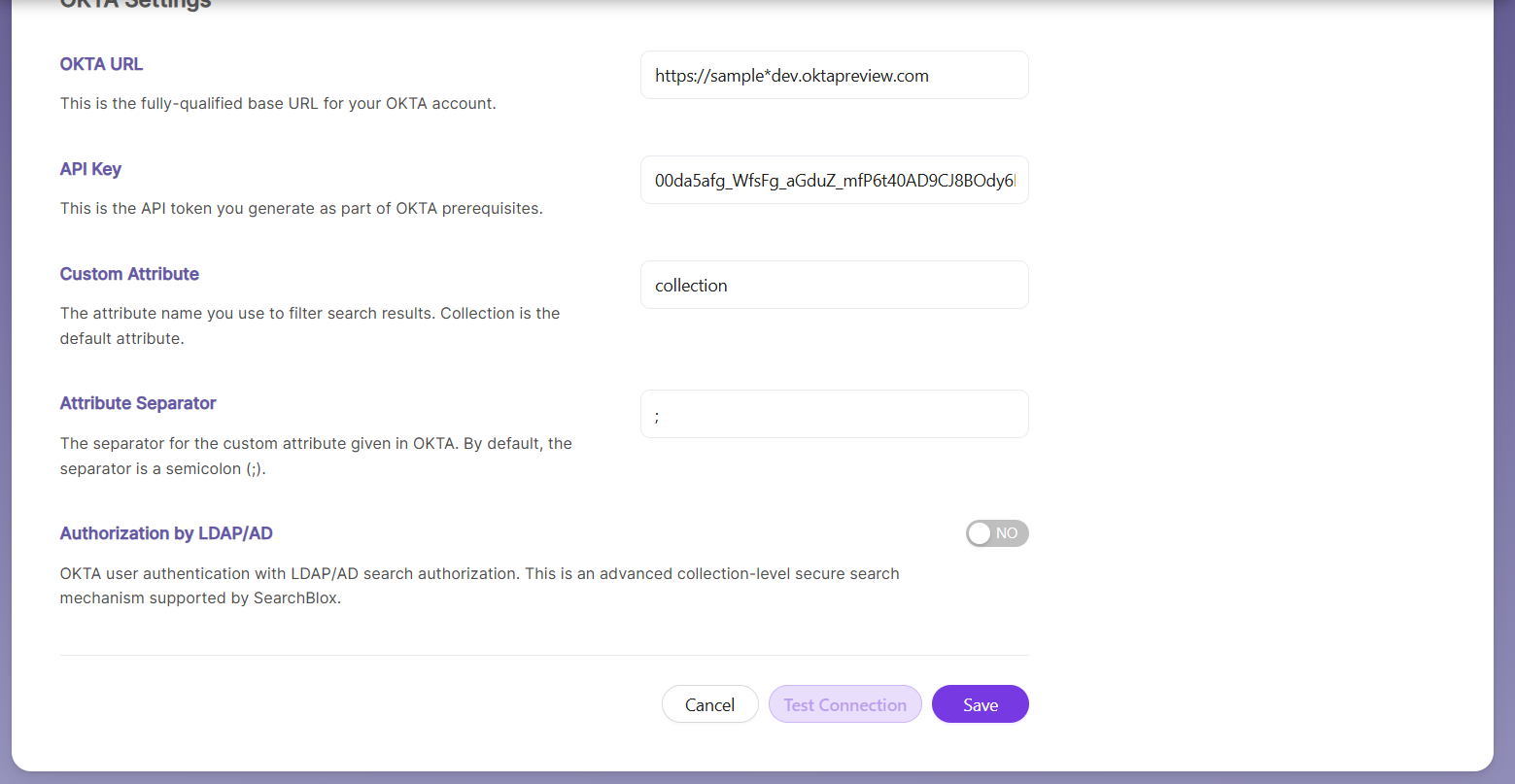
| Attribute Separator | The separator used for attributes defined in OKTA. |
| Authorization by LDAP/AD | Allows OKTA user authentication while using LDAP/AD for search authorization. This advanced security option is supported at the collection level. |
- Save the OKTA Settings and Test the connection.
Configuration and API token
- Login to OKTA
- Allows OKTA to handle user authentication while LDAP/AD manages search authorization. This provides an advanced security option that works at the collection level.
http://developer.okta.com/docs/api/getting_started/getting_a_token.html
-
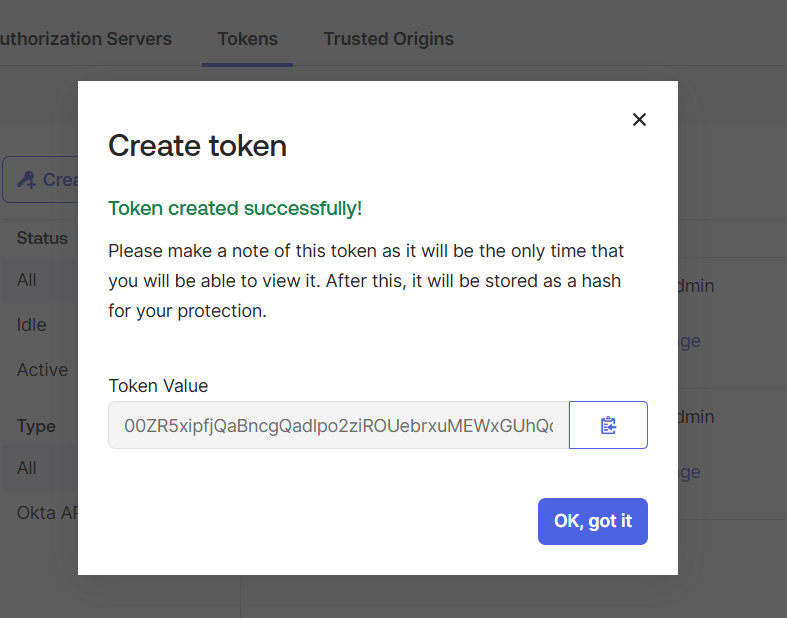
**Please save this token locally, as you will not be able to view it again.
-
Use this token in the OKTA settings by going to Dashboard → Security and selecting Security Setting as Private.
- On testing the connection, it should be successful.
Important Note:
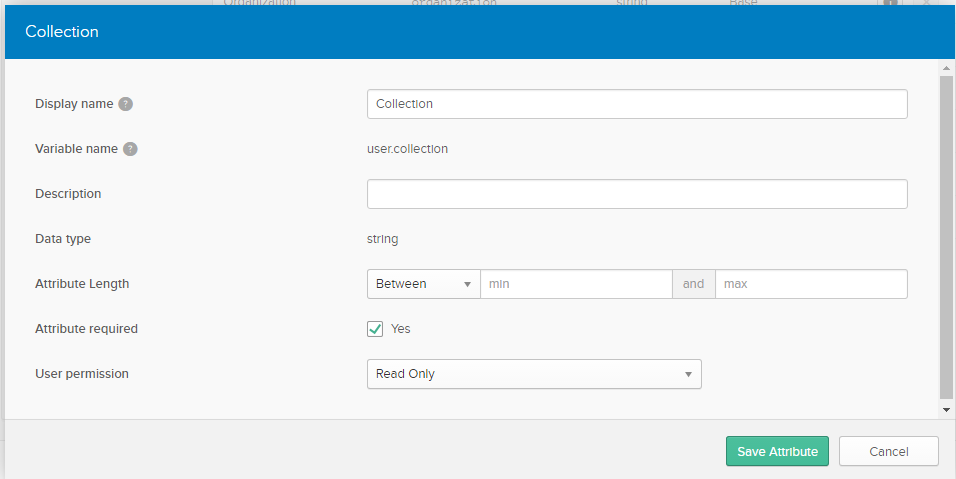
- If you are setting up OKTA for SearchBlox for the first time, please set up your collection attribute mentioned below and then try testing the connection.
Setting up collection attributes
- Navigate to Directory/Profile Editor.
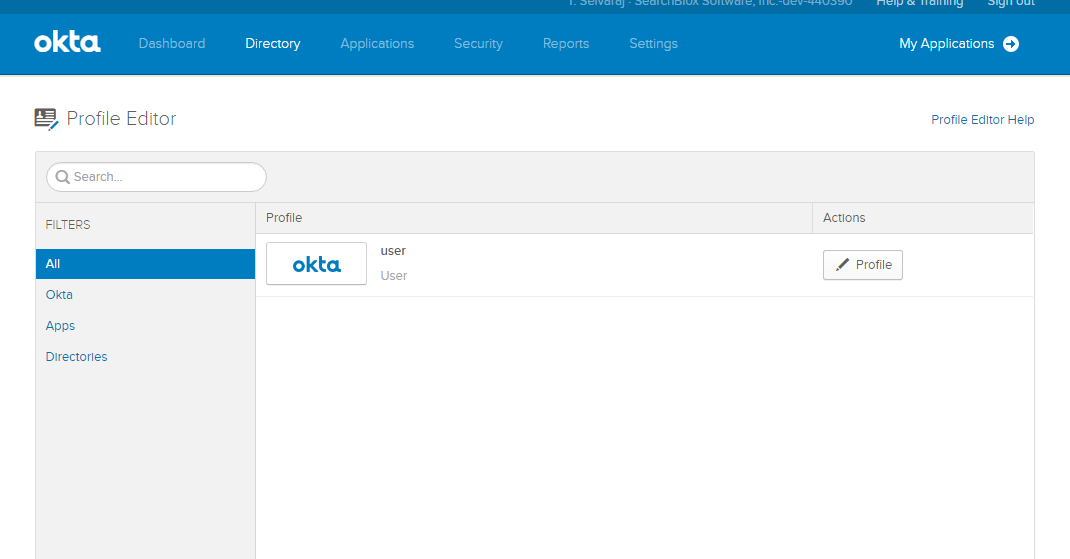
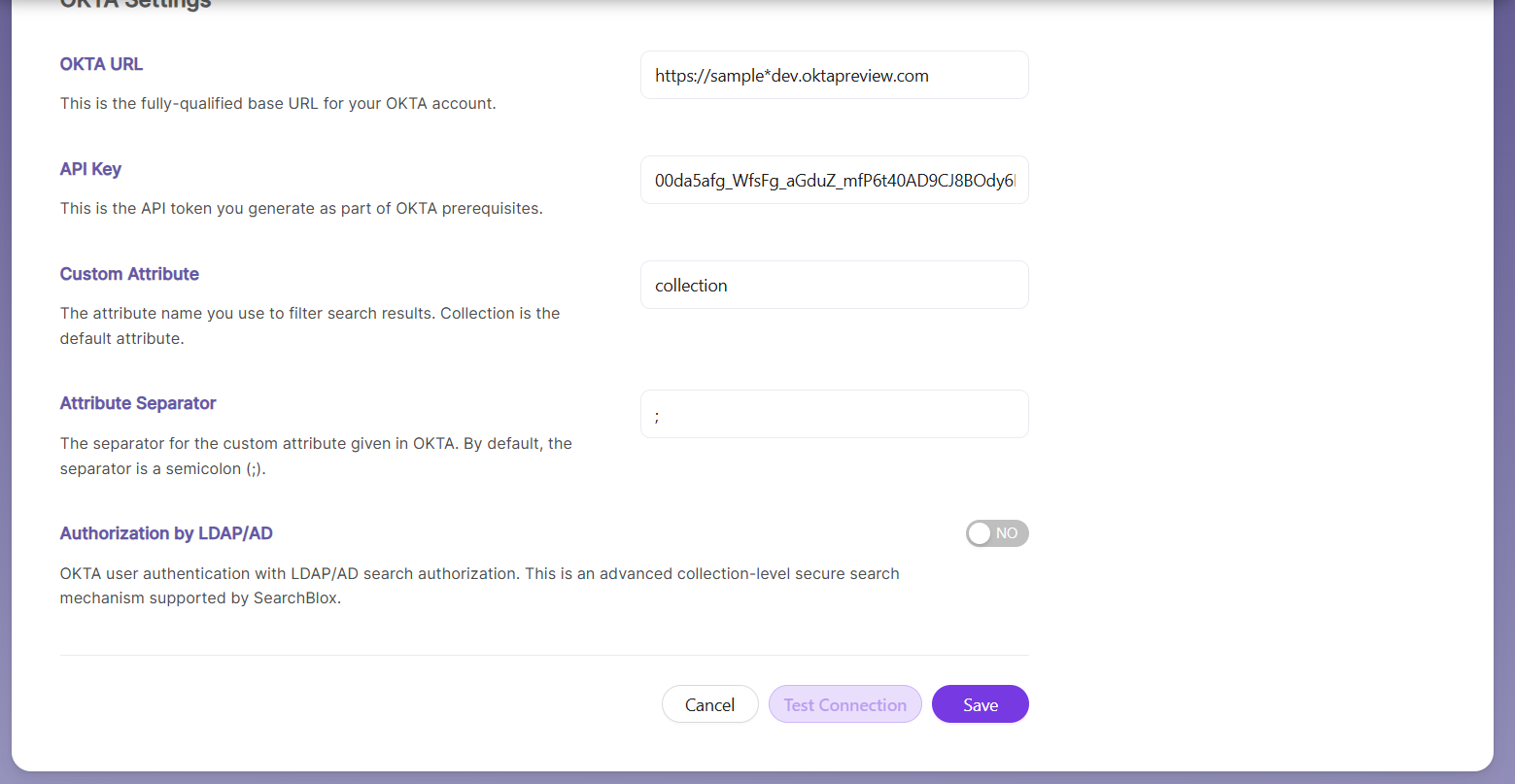
- Edit the OKTA profile and add a new attribute named “collection” (or any other preferred name). This is a user-level profile attribute, so whenever a new user is created, the collection attribute will appear in their profile.
Limiting collections based on users
- Once the attribute is created, you can assign collection access based on each user’s permissions.
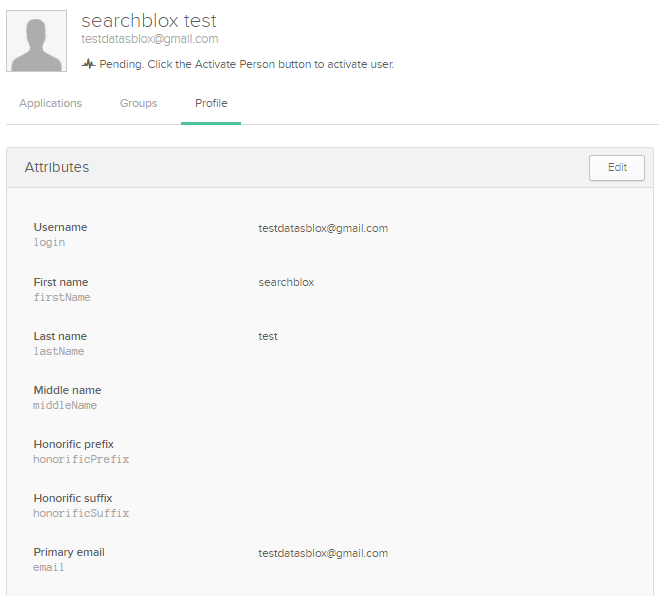
- To give user1 access to collections 1 and 2, go to Directory → People, select the user, and open the Profile tab.
- In the user’s profile, set the collection attribute to control which collections they can access.
- If you set the attribute value to 1:2, the user will have access only to collections 1 and 2, where : is the attribute separator configured in the SearchBlox OKTA secure search settings.
- In the SearchBlox OKTA settings, custom attributes and attribute separators work as follows:
Custom Attribute: This is the collection attribute created earlier to filter collections for each user.
Attribute Separator: This separates the collection IDs. For example, if the collection value is “1:2:3”, the separator is “:”. Use this format to define which collections the user can access.
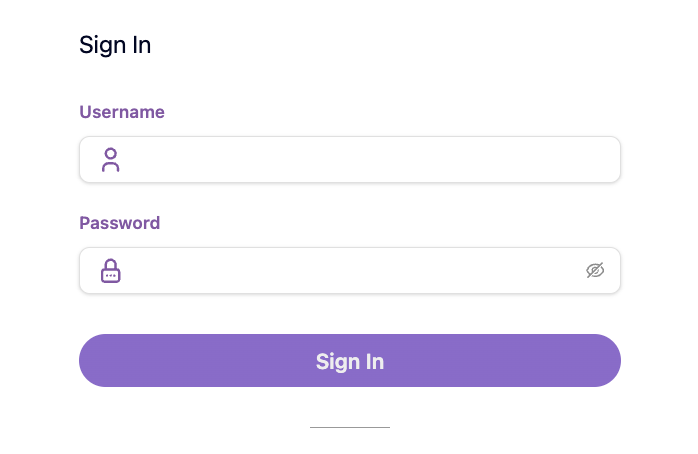
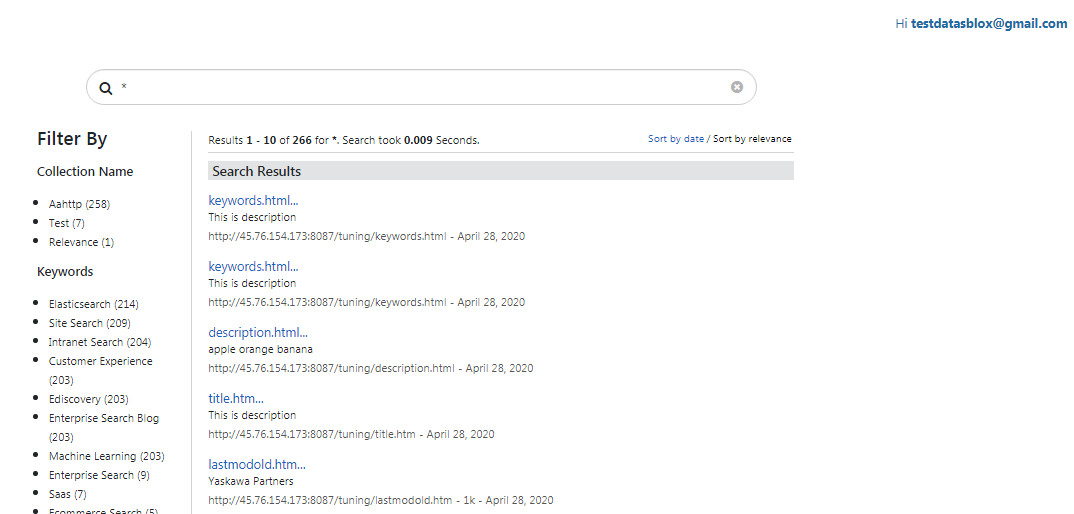
Accessing Secure Search using OKTA
You can log in using OKTA credentials and perform a secure search from this link:
https://localhost:8443/search/index.html.
OKTA SSO with LDAP Authorization
Create an OKTA SSO
- Signup for OKTA (https://developer.okta.com/signup/) using React Stack for SearchBlox (If you have an OKTA account ready, please skip this step and login to your OKTA account)
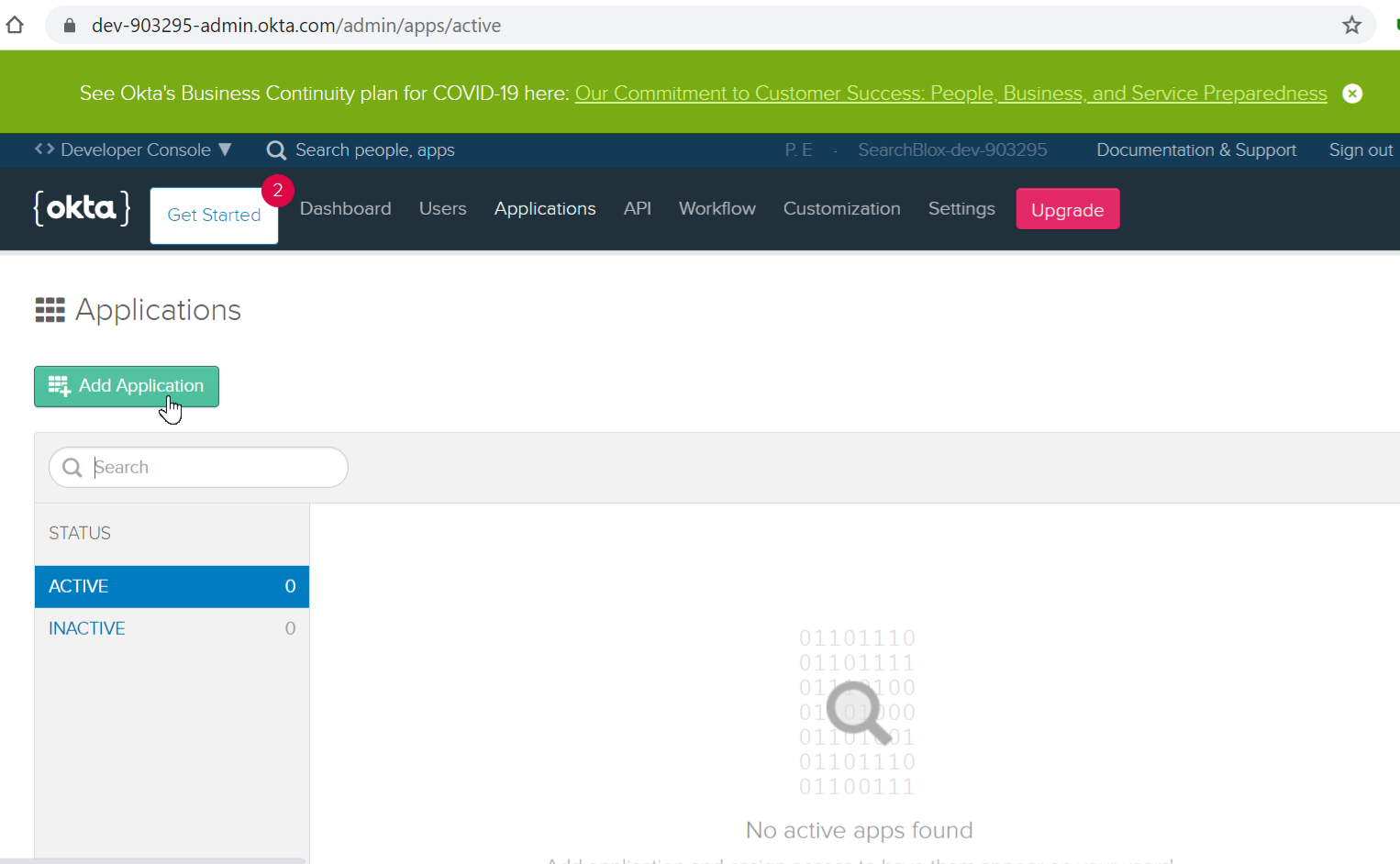
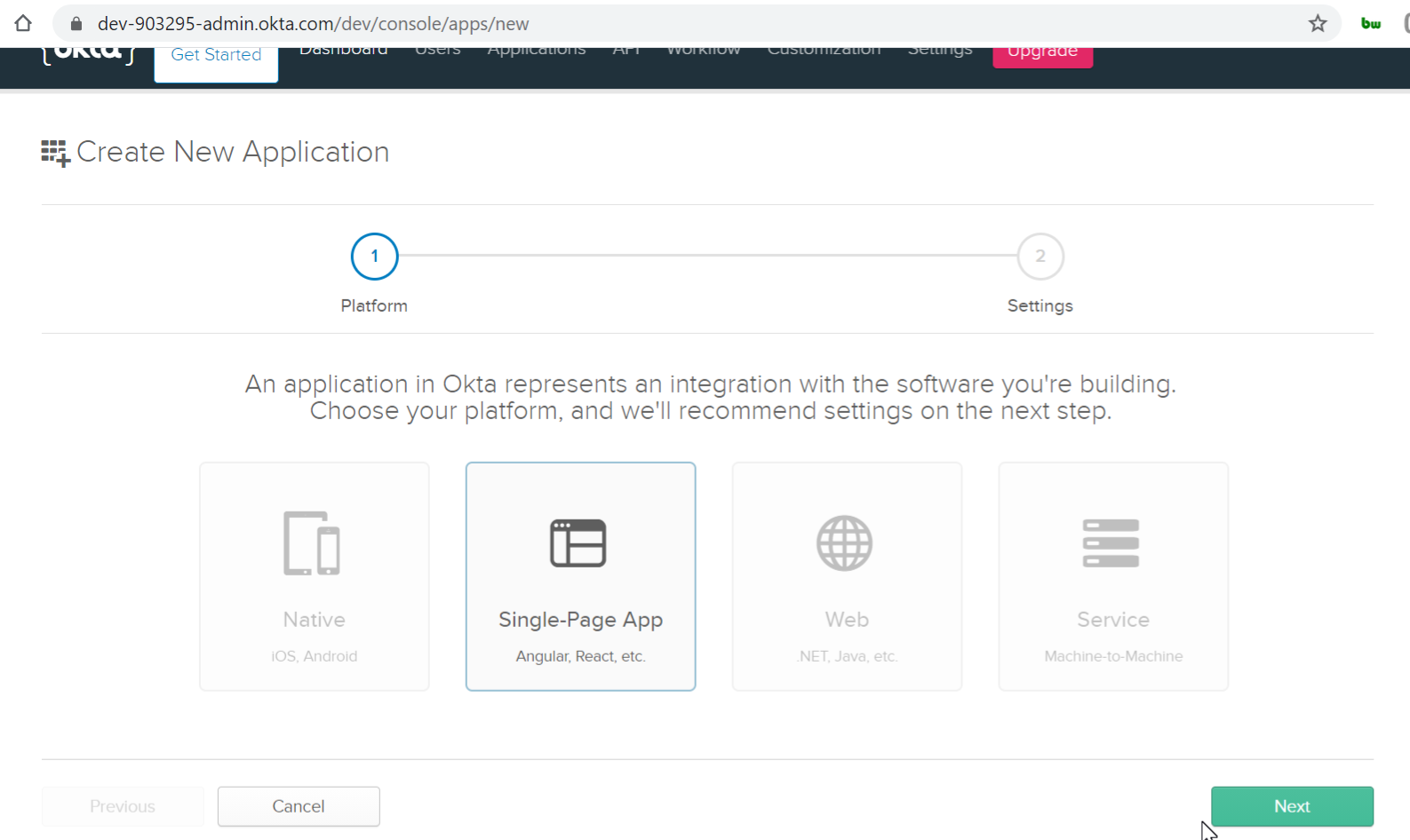
- Go to the Applications tab and click Add Application. Select Single Page App and then click Next.
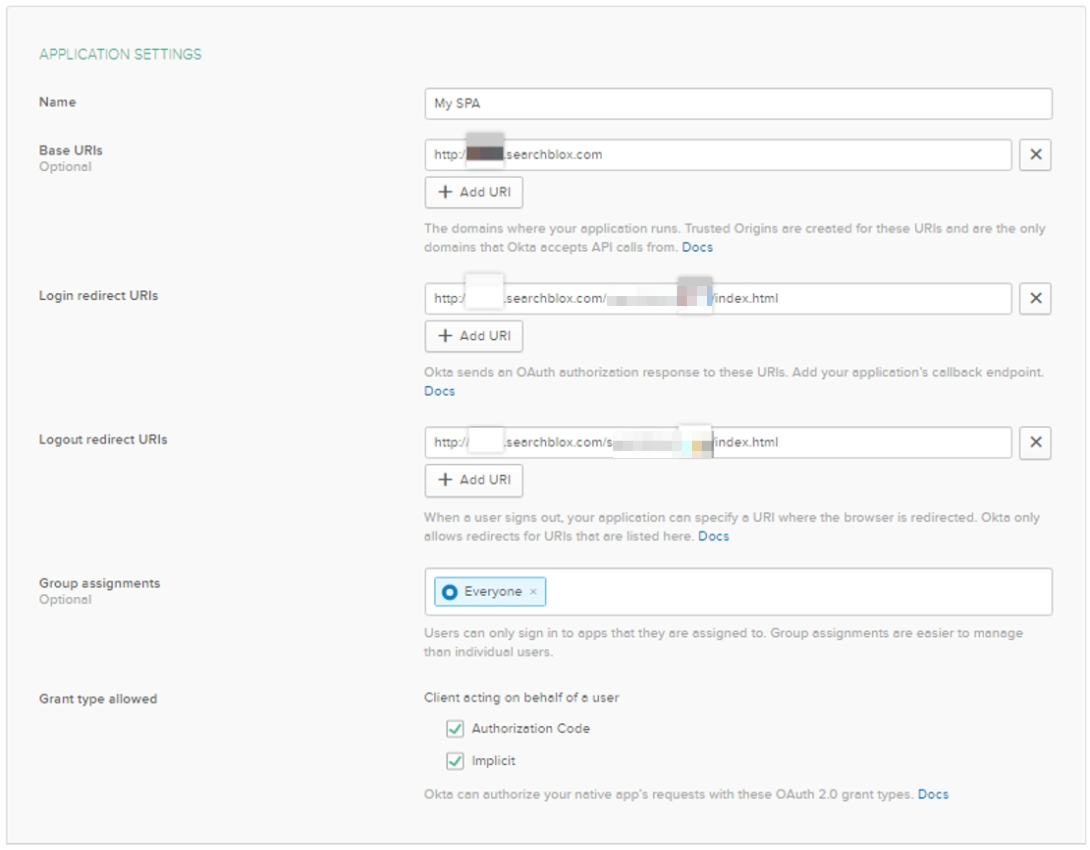
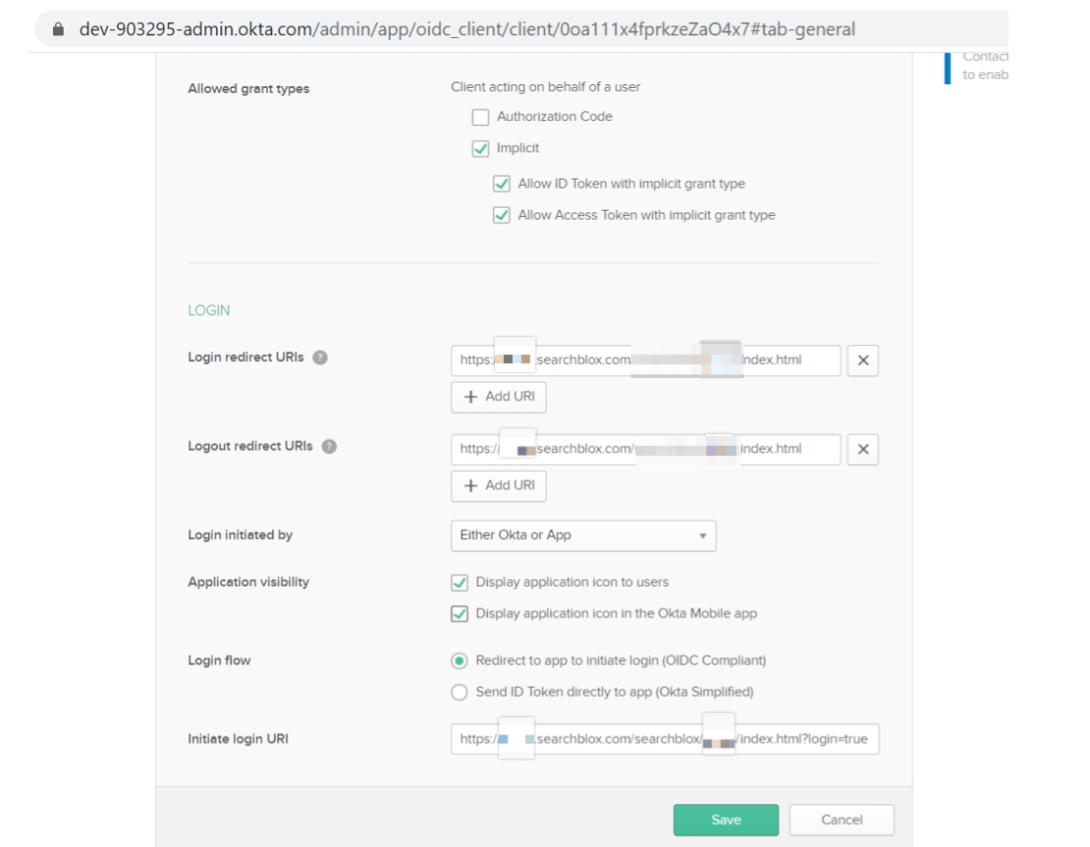
- In the Application Settings, enter the Application Name, Base URIs, Login Redirect URIs, and Logout Redirect URIs. Select the Implicit checkbox and click Done. The Authorization Code option is selected by default.
For example:
Base URI – https://test.searchblox.com
Login Redirect URI – https://test.searchblox.com/plugins/test/index.html
Logout Redirect URI – https://test.searchblox.com/plugins/test/index.html
-
- Click **Edit** in the General Settings and set the **Initiate Login URI**. Enable **Allow ID token** and **Allow Access token**. Select **Either OKTA or APP** under _Login Initiated By_. After completing these steps, click **Save**. For example: **Initiate Login URI** –
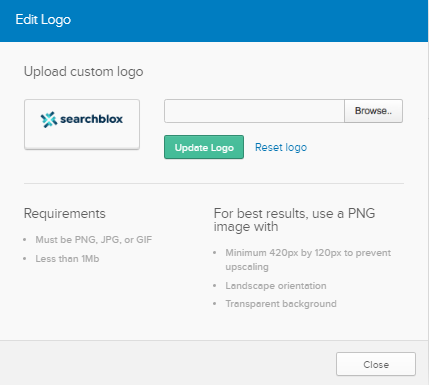
- You can also add a logo for the application you created. Click the edit icon, choose Browse, select the desired file, and then click Update Logo.
Click HERE to download the SearchBlox logo as shown below.
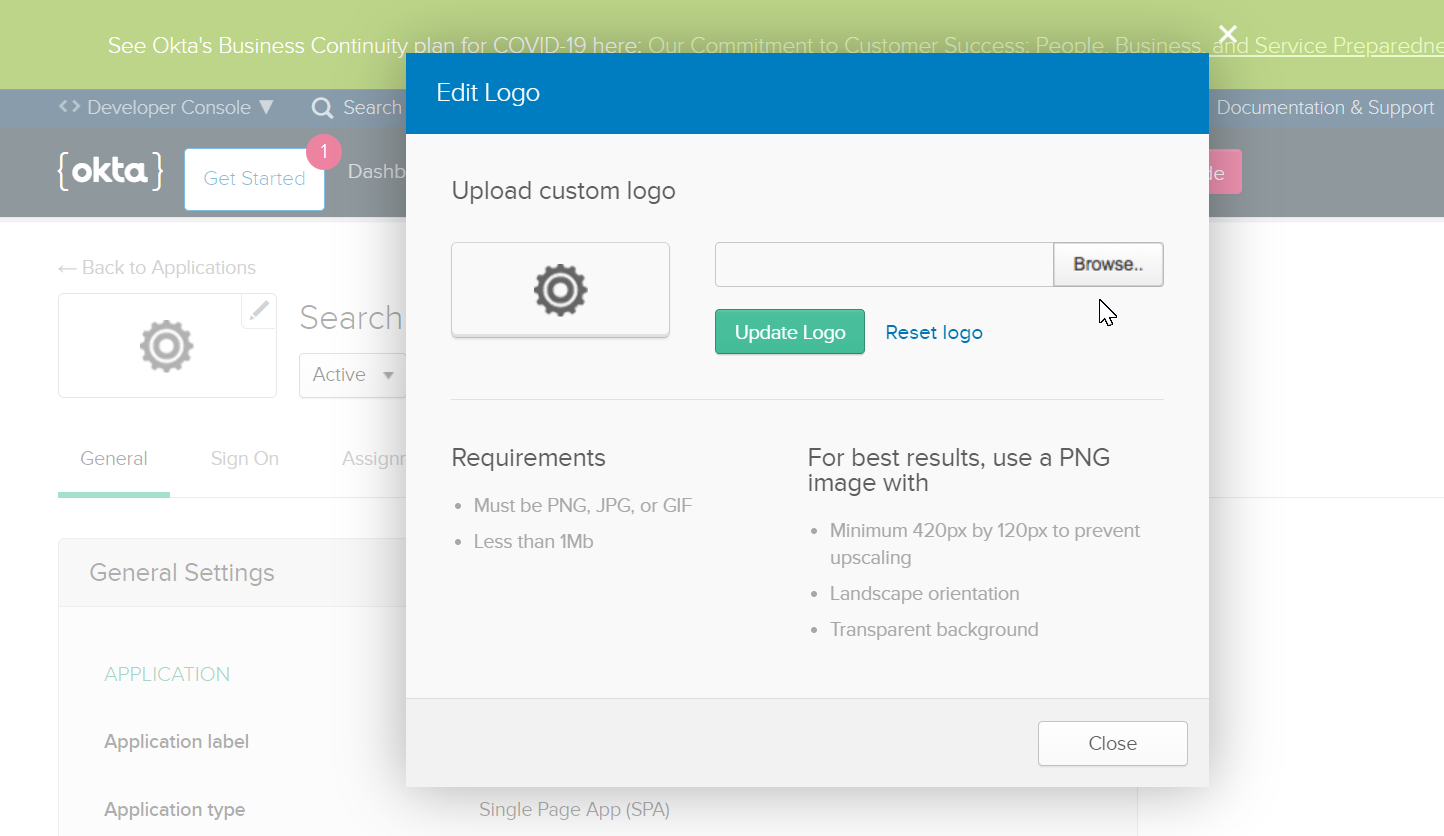
- Once you update the SearchBlox logo, the application chiclet will appear as shown below.
Add Users/Group Claims
- Once the application is successfully configured, you can add Users or Group Claims.
- To add a new user, go to People under the Users tab. Click Add Person, enter the required details, and either set a password as an admin or allow the user to create their own password.
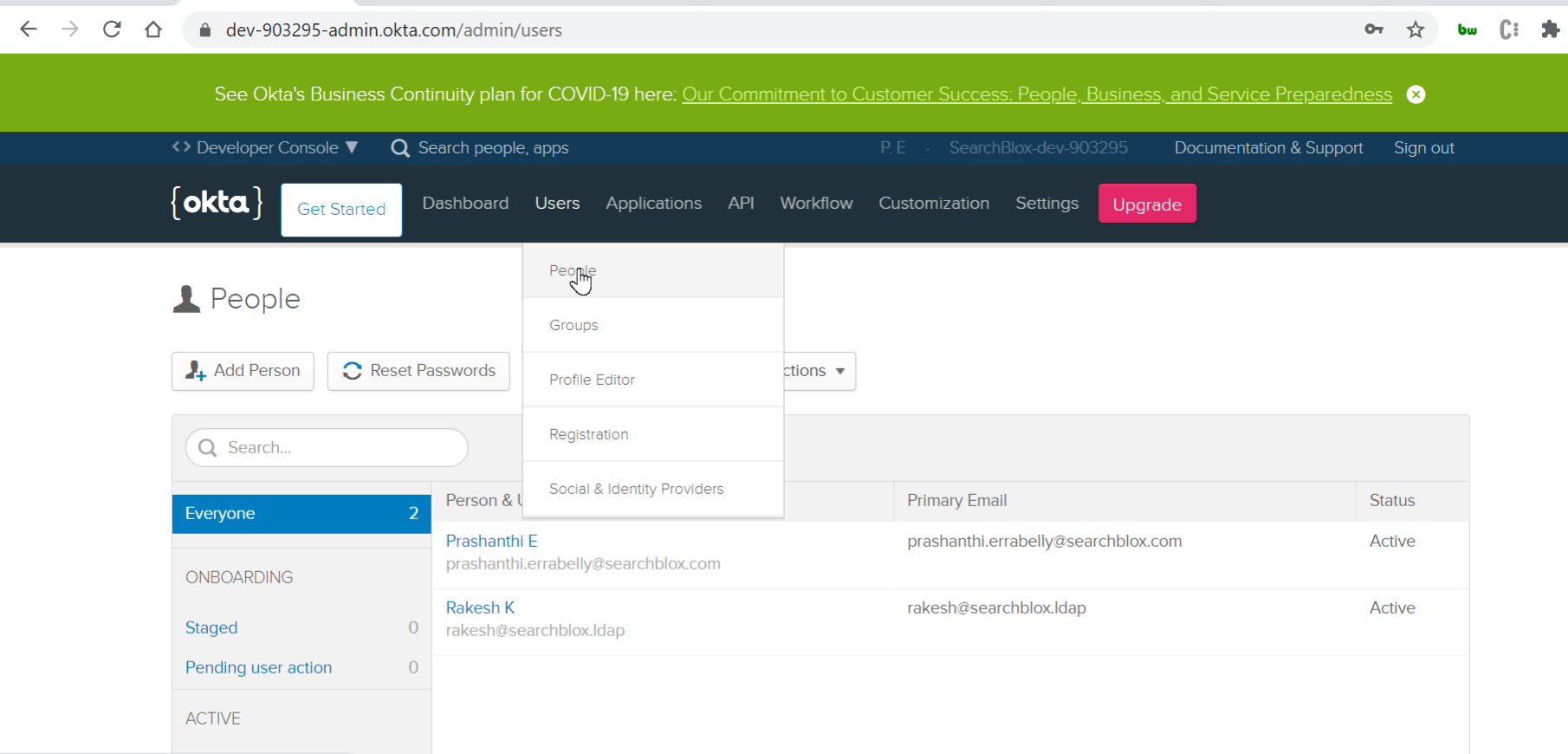
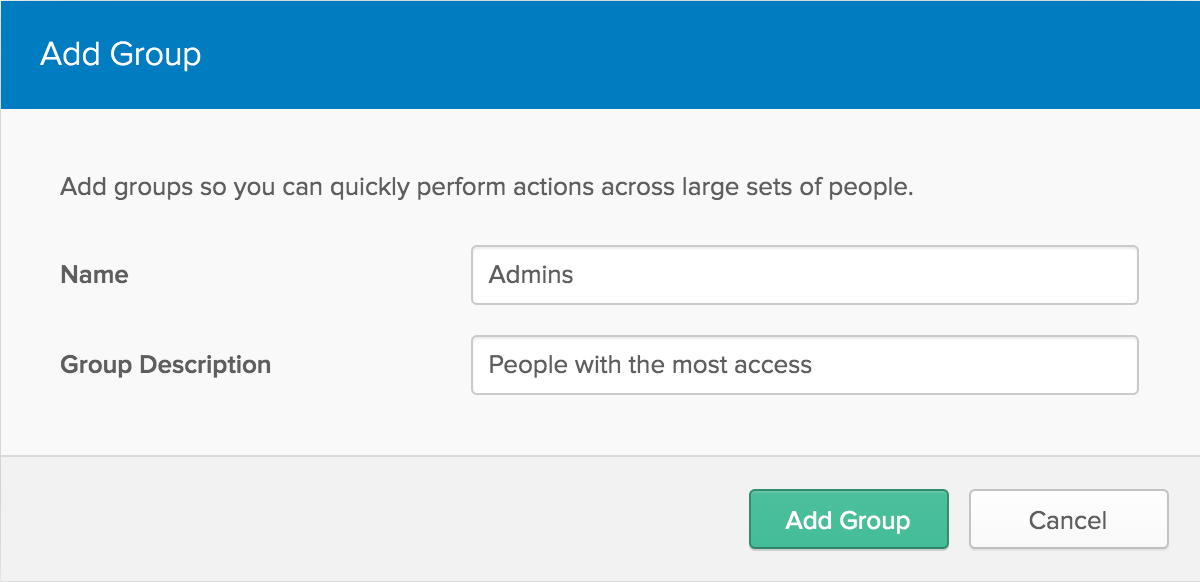
- To create a new group, go to Groups under the Users tab. Click Add Group, enter the name and description, and then add users to the newly created group.
- Add your SearchBlox OKTA Users to the created group.
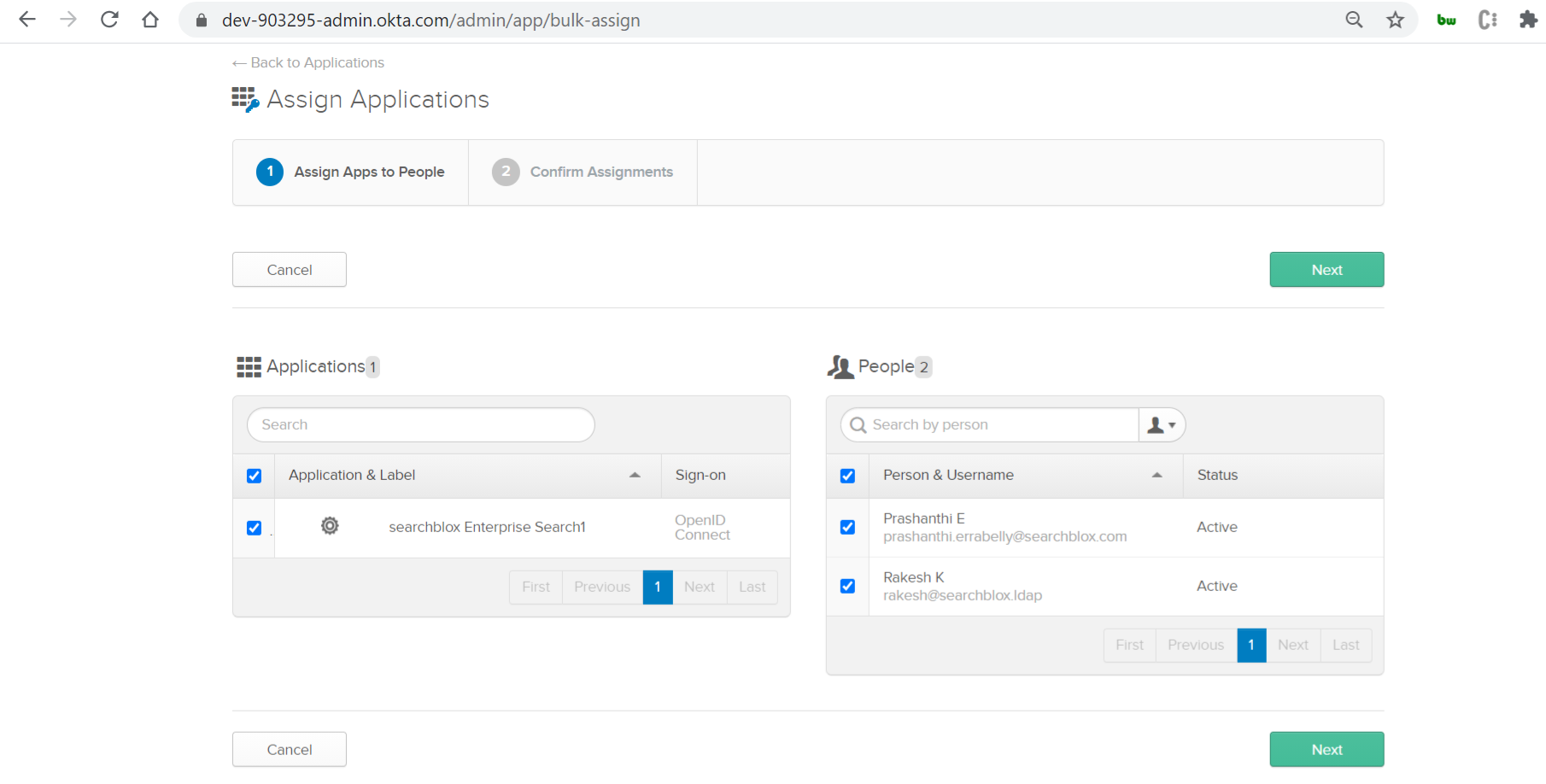
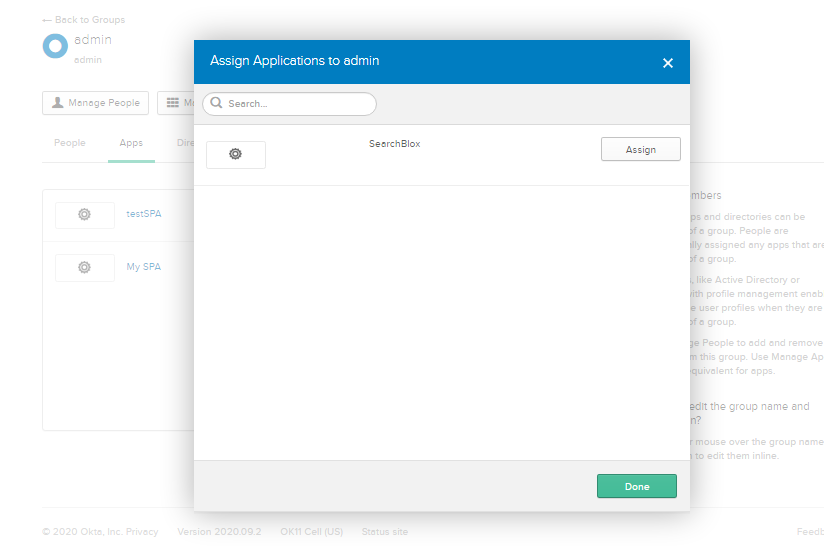
- To assign the application to a group, click the group name, select Manage Apps, click Assign on the application, and then click Done.
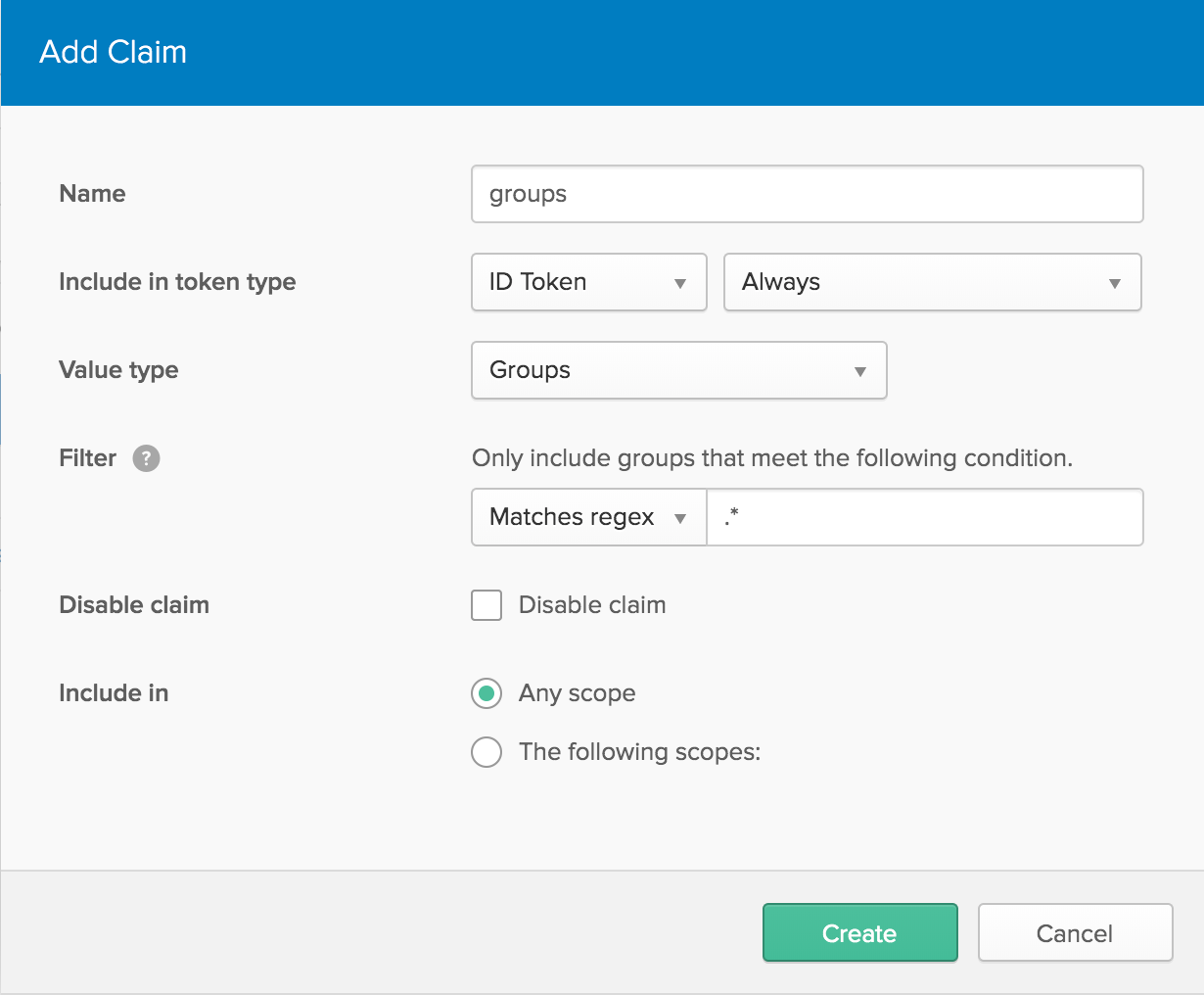
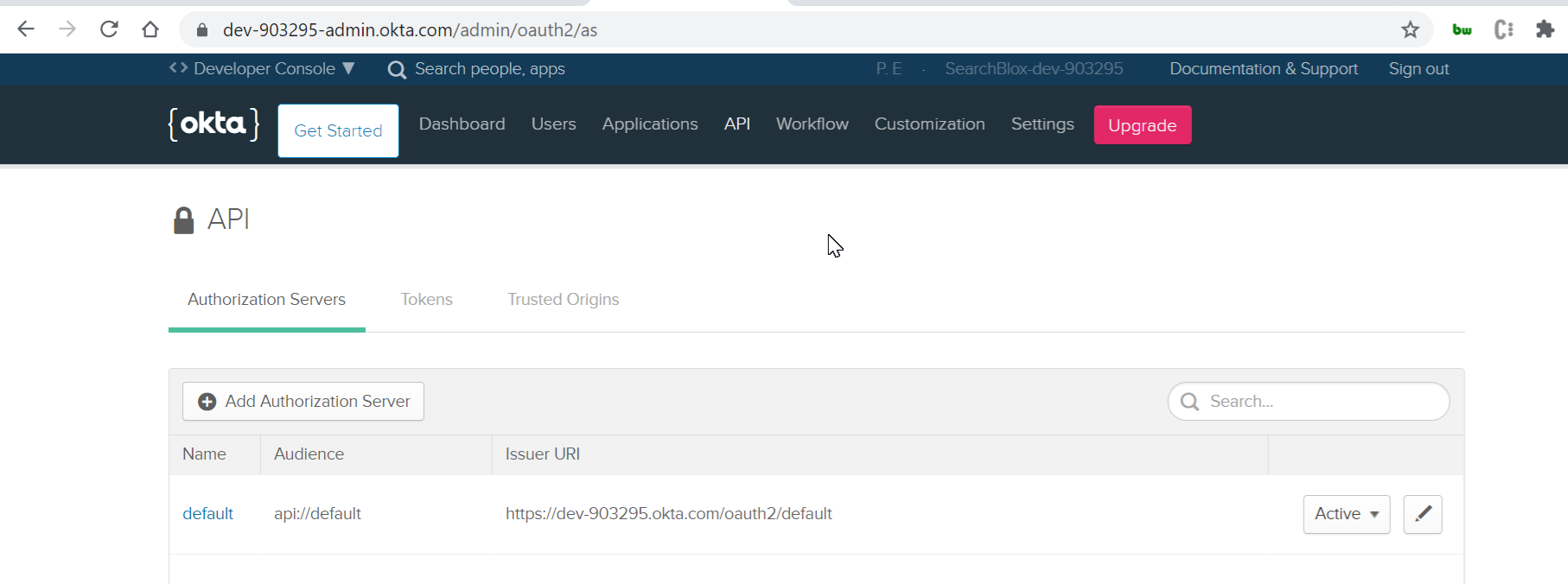
- To add Claims, go to Authorization Servers under the API tab. Select the default server, then open the Claims section.
- Click Add Claim, provide a name, change Include in token type to ID Token, set Value type to Groups, and set the filter to Matches regex with the value .*. Once finished, click Create.
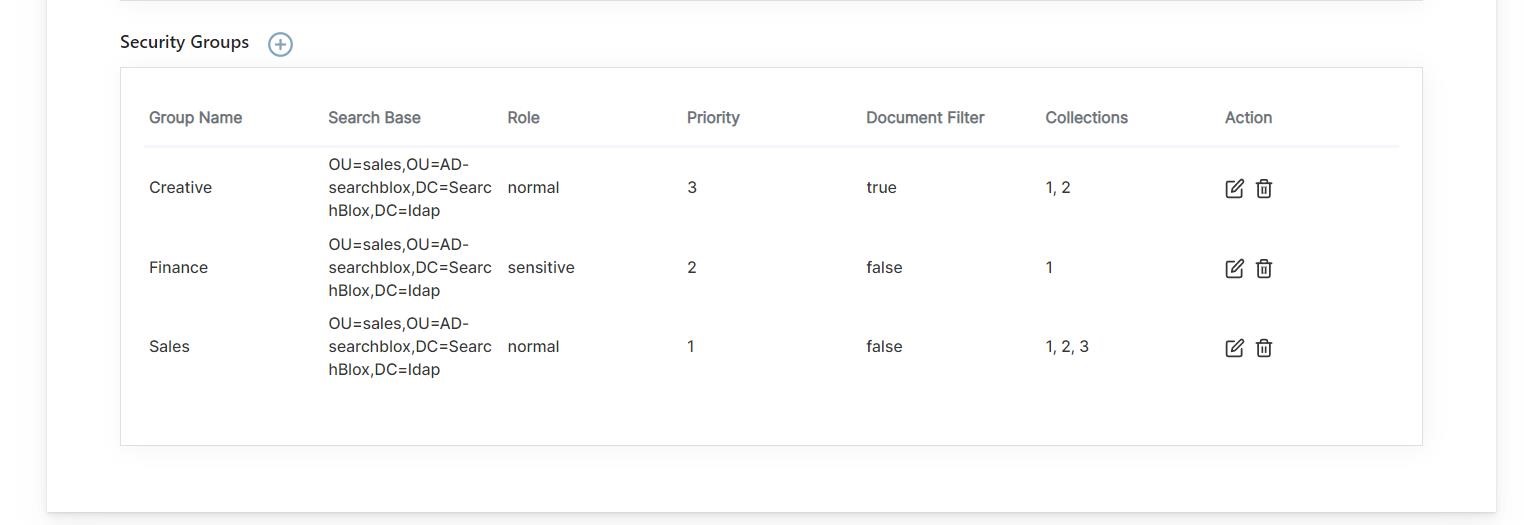
- Log in to your SearchBlox Admin Console and configure your LDAP settings and security groups. After that, set up your OKTA configuration.
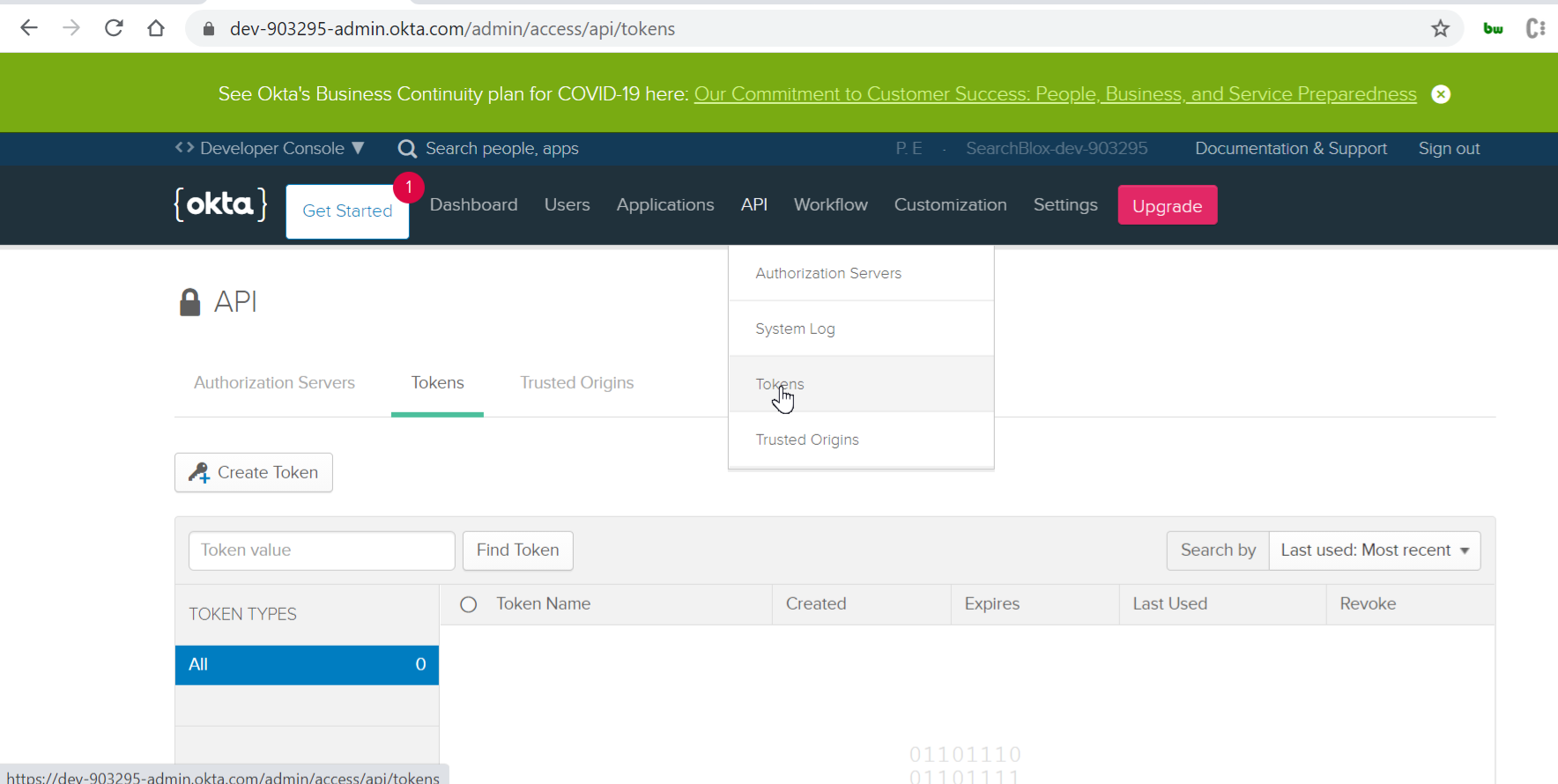
To generate the OKTA API token, go to Tokens under the API section and click Create Token.
- Configure OKTA in SearchBlox Admin Dashboard > Security, and set Security Settings to Private.
- Click Test Connection in both LDAP and OKTA to confirm that the configurations are successful.
Configure Custom UI
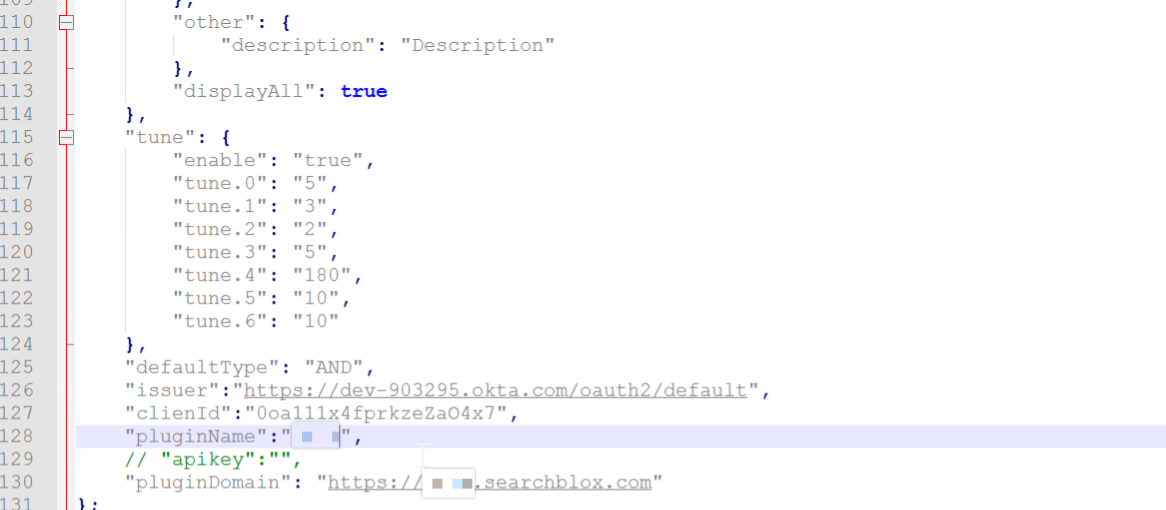
- Download the SearchBlox Custom UI plugin (provided upon request). Extract the file and update the facet.js file.
- Modify the Issuer URI, ClientID, Plugin Name, and Plugin Domain values in the facet.js file based on your OKTA setup.
- To find the Issuer URI, go to Authorization Servers under the API tab.
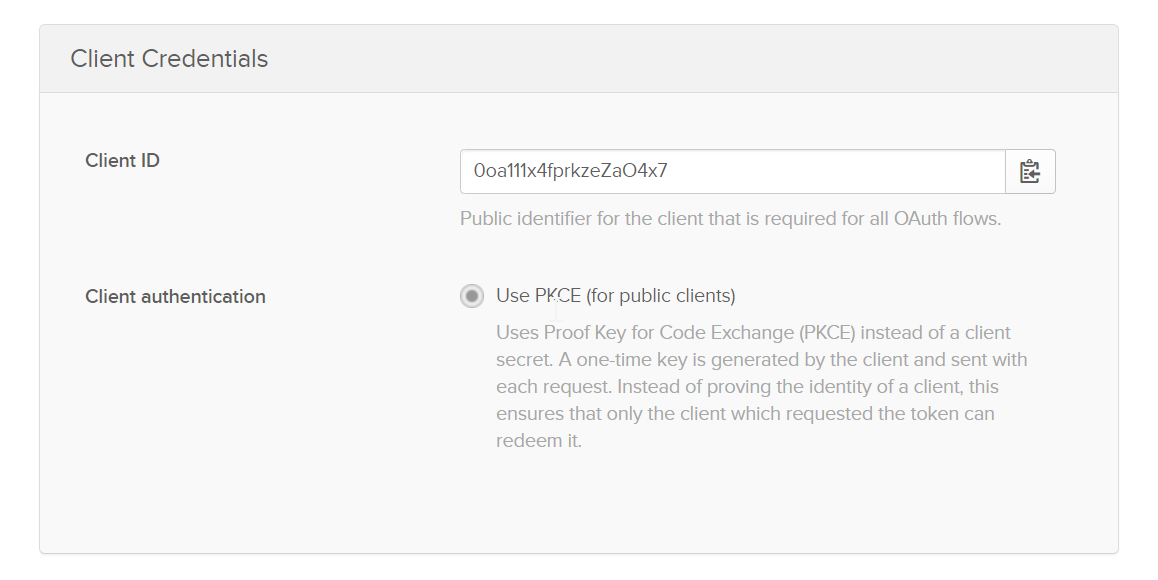
- To find the ClientID, open your OKTA SearchBlox application and check the General tab under Client Credentials.
- After making the required changes, save the updated facet.js file. Then copy the Custom UI folder into:
<SearchBlox-Installation-Directory>/webapps/ROOTS/<custom-ui-name>/
- You can now access the SearchBlox Custom UI using valid users to test OKTA SSO. A valid user will be able to access only the private collections assigned through LDAP security groups, along with any public collections if available.
Note:
- Private collections are accessible only through secure search authentication.
- Public collections can be accessed with or without secure search authentication.
- Make sure to whitelist your SearchBlox domain to avoid CORS errors when accessing the Custom UI. Click HERE for instructions.
- Secure search logs are stored in the securesearch.log file located at webapps/ROOT/logs.
- Configure LDAP/AD Realm Security Groups before integrating with OKTA. OKTA can be set up by enabling Authorization by LDAP/AD.
- When an OKTA user logs in, secure search handles authentication, and LDAP handles authorization.
Updated about 2 months ago
