LDAP/AD Realm
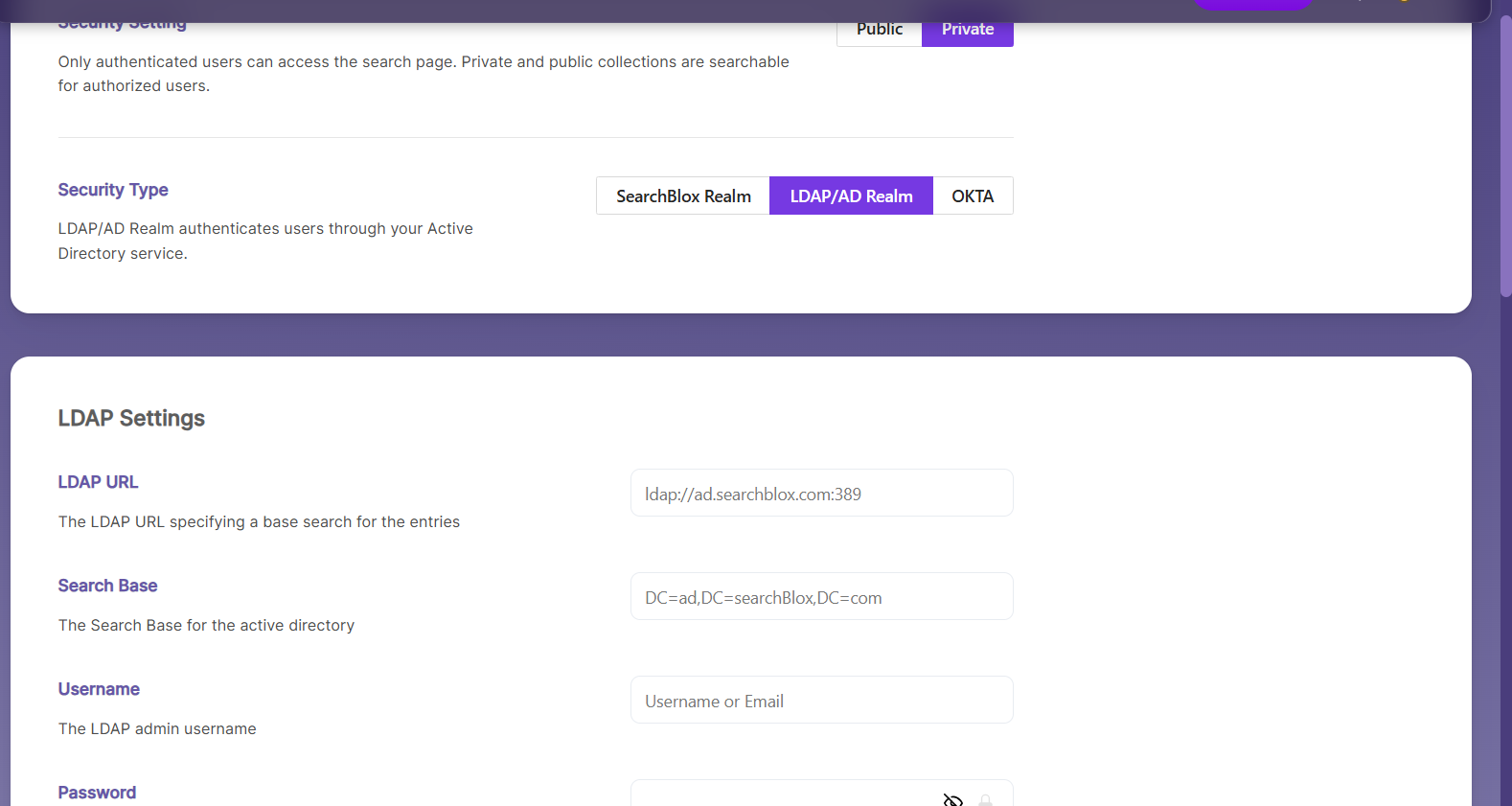
Secure search can be enabled using LDAP/Active Directory by selecting the LDAP/AD Realm checkbox and entering the required configuration settings as shown.
LDAP Settings
- Select LDAP/AD Realm
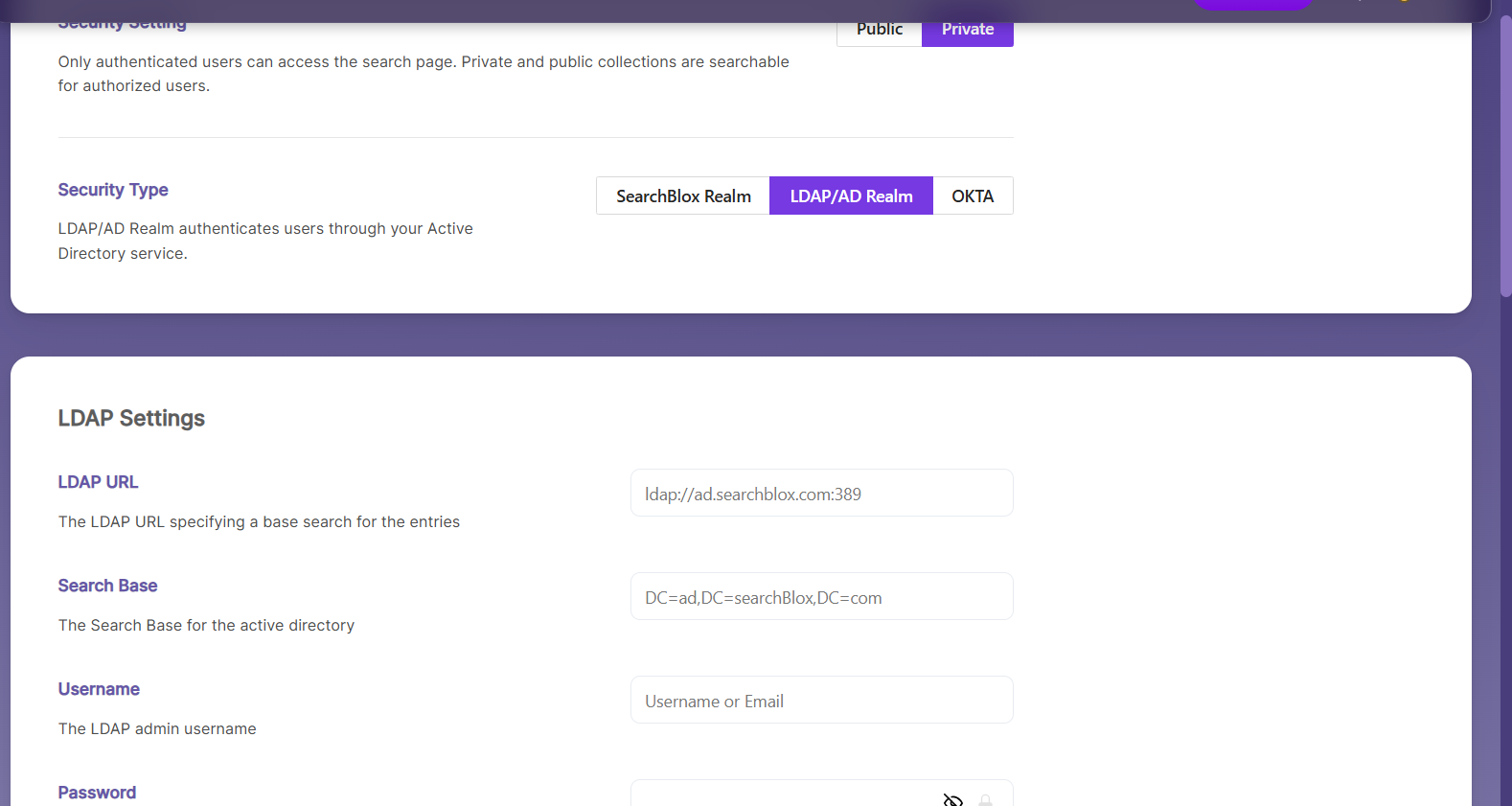
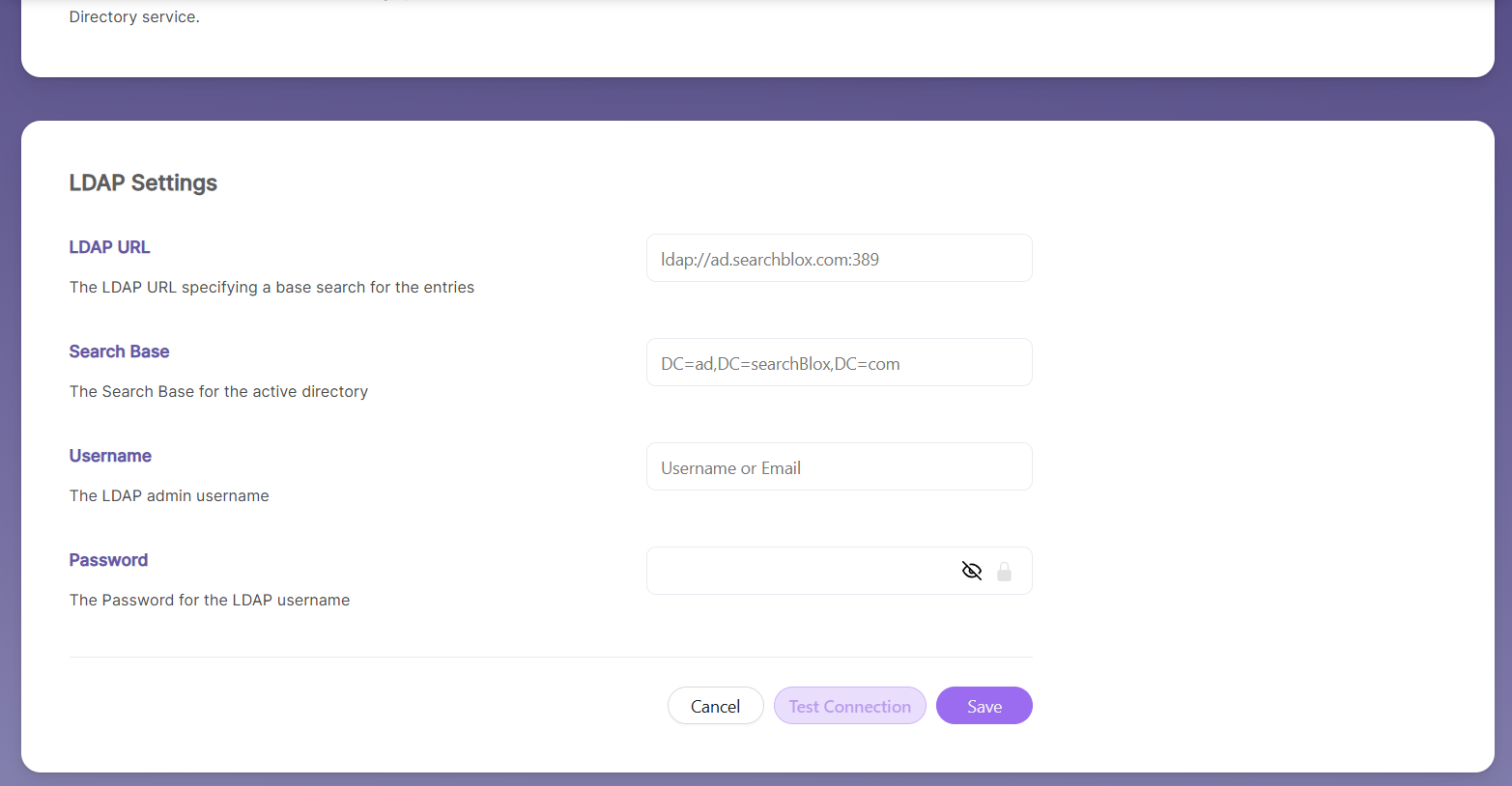
- Give the required LDAP details
| Field | Description |
|---|---|
| LDAP URL | LDAP URL that specifies a base search for the entries |
| Search Base | Search Base for the active directory |
| Username | Admin username |
| Password | Password for the username |
- Test the connection. If the connection is successful, you will see the confirmation message shown below.
Add Security Group
- Using this setting, you can configure security group settings for LDAP or Active Directory.
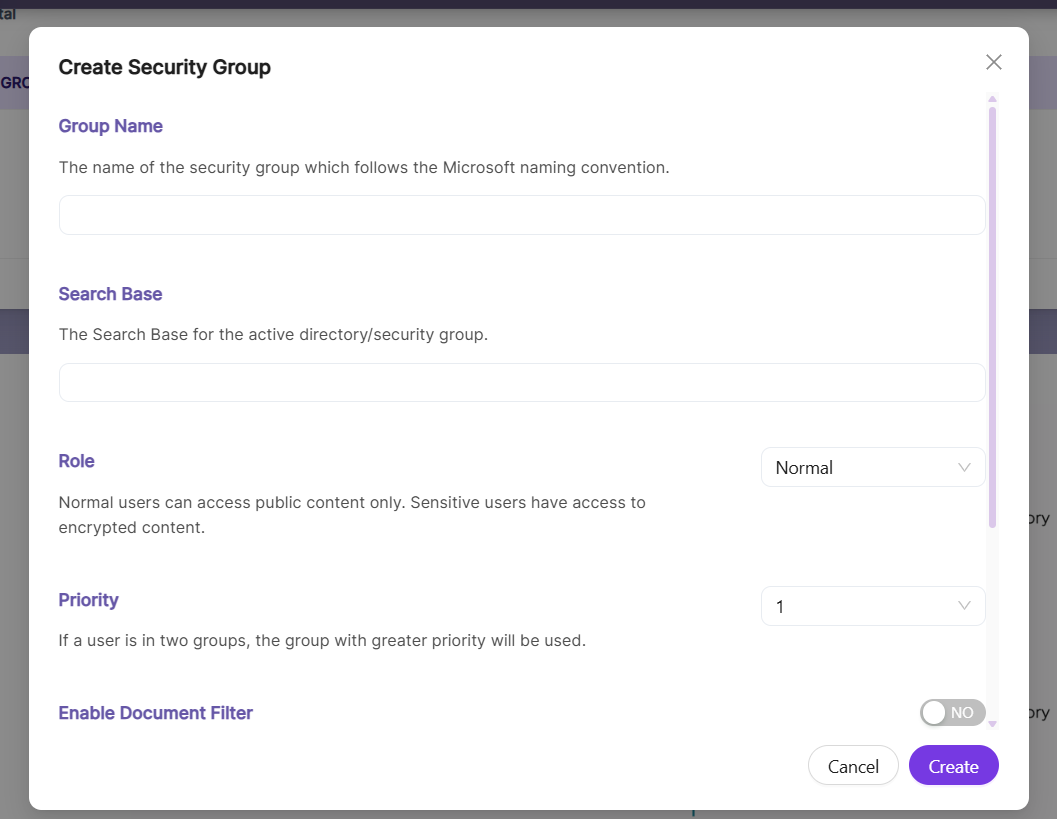
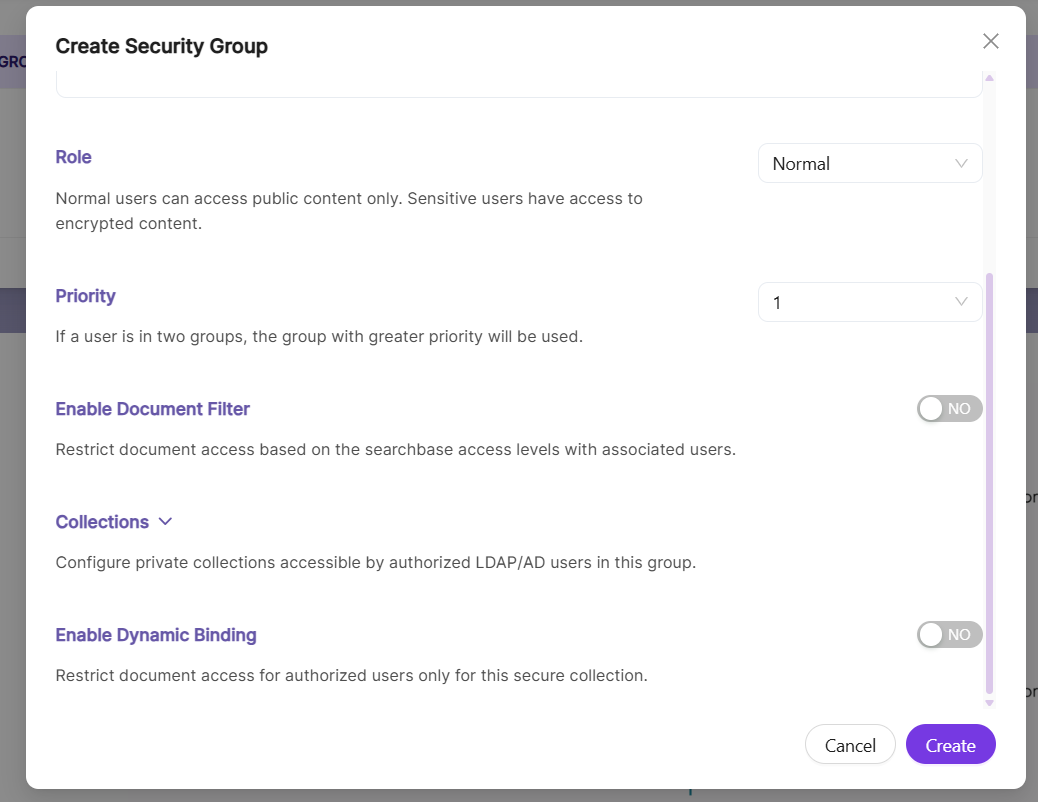
- Enter the required parameters for the LDAP Security Group. The details of each parameter are explained in the following table:
| Field | Description |
|---|---|
| Group Name | This is the name of the security group. You can define it based on your organizational unit (OU) or requirements. The Group Name must contain alphanumeric characters, with a minimum of 3 and a maximum of 50 characters. The only special character allowed is the underscore. |
| Search Base | This defines the search base for the Active Directory or security group. |
| Role | You can select either Normal or Sensitive. The default value is Normal. Users marked as Sensitive can access encrypted content throughCollection Encryption |
| Priority | This defines the priority level of the group. Use case: If a user belongs to two groups, the group with the higher priority value will be considered the user’s active group. |
| Collections | This lists the collections that users in the group can access. |
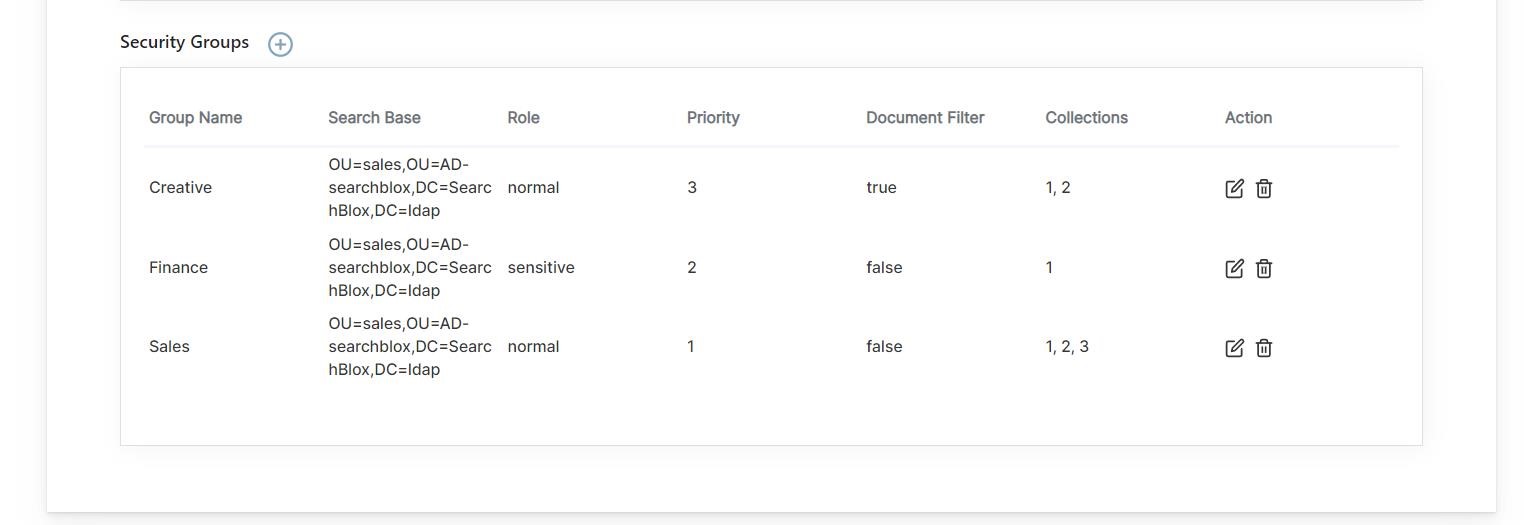
- After adding the groups, you can view them in the Security User Groups dashboard.
Features of Security Groups in LDAP Realm
Group Settings
- After configuring the LDAP settings, you must provide the Group settings to integrate collection-based security with LDAP for search results.
- When creating a group, you can assign specific collections to it. Users in that group will have access only to the assigned collections.
- Users who belong to the corresponding Organizational Unit (OU) will be included in the group.
- You can create multiple groups for the same Organizational Unit (OU).
- The permissions and users for a group are retrieved based on the search base provided, making it a critical parameter when creating a Security User Group.
Group Naming
- LDAP security groups can be named following Microsoft’s naming conventions, which allow the use of special characters.
- As noted in Microsoft’s documentation, an LDAP distinguished name is globally unique. For example, the distinguished name for a computer named mycomputer in the MyOrganizationalUnit organizational unit within the microsoft.com domain is: CN=mycomputer, OU=MyOrganizationalUnit, DC=microsoft, DC=com.
- For instance, a valid group name following this convention is: A602-AC-DMASFS2_sdata RW.
Priority
- When a user belongs to two groups, the group with the higher priority is applied. For example, if a user belongs to Group A with priority 5 and access to Collection 1, and also belongs to Group B with priority 3 and access to Collection 2, the user will be placed in Group A because it has the higher priority. As a result, the user will have access only to Collection 1.
Sensitive User
- Only users with the Sensitive role can view encrypted content. For more details on encryption. Please refer Collection Encryption .
Accessing Secure Search for LDAP Realm
Log in using LDAP/AD credentials here:
https://localhost:8443/search/index.html
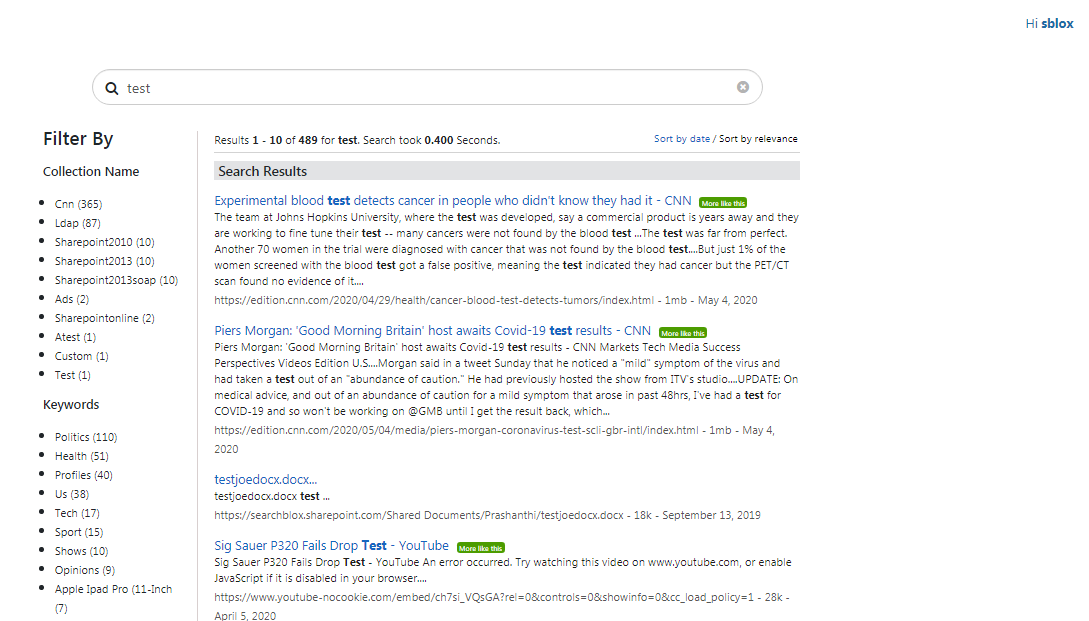
Then perform the secure search.
Updated 3 months ago
What’s Next
